|
Protecting Your
Ports
This is a one of the best ways of securing your machine, if you
prevent certain ports from being accessible from people outside
your private network (LAN) then there is less chance that they will
be able to gain access or cause problems (i.e. via flooding or DoS
attacks etc.). To prevent ports from being visible to the outside
world you will need to modify your firewall or even better yet you
can download an secure firewall script and then modify it to allow
the things you want to allow.
In the previous
Setup and Sharing section of this site we described a very simple
method of firewalling, this was just using the default action of
DENY, although this is good, its not the best, you can do better.
There are many
comprehensive firewall scripts available on the net that can be
freely downloaded, we will only talk about a couple here:
rc.firewall
Download: http://rcf.mvlan.net/
"rcf
(aka rc.firewall) is an ipchains-based firewall with support for
over 50 network services (including vtun, dhcp, nfs, smb, napster,
proxies, online games, etc.), masquerading, port forwarding, and
ip accounting. All services are self-contained modules which can
be prioritized in the ipchains stack. Protections include spoofing,
stuffed routing/masqerading, DoS, smurf attacks, outgoing port scans,
and many more. rcf also supports unlimited public, private (masqu'ed),
dmz, and mz (non-masq'ed) interface and their subnets. Access rules
are defined per interface and dmz/mz server "clusters". rcf is compatible
with Red Hat, Slackware, Debian, Linux Router Project (LRP), and
many other distros. rcf is distributed under the General Public
License (GPL) terms."
As with most
Linux things rc.firewall comes in both a tarball version (rcf-5.1.tar.gz)
and a rpm version (rcf-5.1-1.noarch.rpm)
for those of you with Red Hat and any distro that supports RPM technology.
Below is the
instructions for installing the tarball version, to install the
rpm just type rpm-ivh rcf-5.1-1.noarch.rpm
and then you can configure it as below.
INSTALLATION:
1. Untar the package by typing tar
xzvf rcf-5.1.tar.gz.
2. Next, cd into the directory it creates, e.g. cd
rcf-5.1/.
3. Read the INSTALL file provided. i.e. cat
INSTALL | more.
4. Run sh install.sh
and follow the prompts, or follow the manual instructions from the
INSTALL file.
5. Edit the appropriate files and start the script. (please read
the rc.firewall site mentioned above for details)
PMfirewall
Download: http://www.pointman.org/
"PMFirewall
is an Ipchains Firewall and Masquerading Configuration Utility for
Linux. It was designed to allow a beginner to build a custom firewall
with little or no ipchains experience."
This firewall
only comes in a tarball version (pmfirewall-1.1.4.tar.gz)
and should support just about any version of Linux according to
their site.
INSTALLATION:
1. Untar the package by typing tar
xzvf pmfirewall-1.1.4.tar.gz.
2. Next, cd into the directory it creates, e.g. cd
pmfirewall-1.1.4/.
3. Read the README and INSTALL files provided. i.e. cat
README | more, cat
INSTALL | more.
4. Run sh install.sh
and follow the prompts.
5. Add you own rules to pmfirewall.rules.local.
6. Start pmfirewall using the path given by the install script.
7. Read the man page.
8. If you wish to see the rules, type: ipchains
-L -n
9. If you have a problem then read the supplied man page. Otherwise
e-mail the creator Rick Johnson.
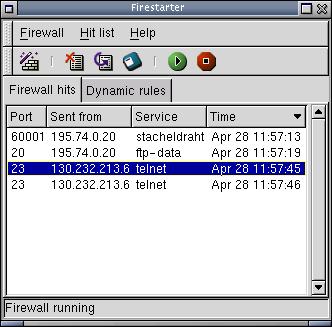
Firestarter
Firewall
Download: http://firestarter.sourceforge.net/
For those of
you who want a GUI based firewall then this is definately your choice,
its easy to install and can be setup by following the simple steps
in the GUI.
"It
features an easy to use firewall wizard to quickly create a firewall.
Using the program you can then open and close ports with a few clicks,
or stealth your machine giving access only to a select few. The
real-time hit monitor shows attackers probing your machine. Firestarter
is made for the GNOME desktop."
You can download
the program in either a RPM (firestarter-0.7.1-1.i386.rpm)
version or a tarball (firestarter-0.7.1.tar.gz),
just use the usual methods to extract them. Firestarte requires
GNOME 1.2 or later and IPChains for 2.2.x machines and Netfilter
for 2.4.x ones.
Below is just
a quick screenshot of Firestarter in action:
Stick's
Firewall
Download: http://www.sticks.f2s.com/
This custom
firewall by Dave Fitches comes in both a IPchains
and IPtables
(for 2.4.x kernels) version, these are definitely worth a visit
if you want to write your own or just get a nice simple to understand
and powerful firewall script.
In order to
use these scripts all you must do is go to the above mentioned pages
and copy the test and paste it into a document on your Linux machine,
e.g. for the IPchains version just copy the text and open pico
filewall.ipchains and past the script into that. You will
then need to chmod +x firewall.ipchains,
now you can run it, or modify it as you need. Please visit his site
for detailed information and setup instructions.
Final notes
and conclusion... CONTINUE
|

